Early Vorlon Adopters Reduce Time to Detect and Remediate Third-Party Risks to Minutes

It’s Time: Emerging from Stealth Mode with Backing from Global VC Firm Accel
Today Vorlon emerges from stealth mode backed by global VC firm Accel. Vorlon has been quietly building a way to secure data in motion. Now, we're ready to share our vision for the future of API security, our story of innovation, and early adopter success.
Current State of API Security Solutions
The API Security industry is entirely focused on securing APIs that an enterprise publishes and neglects those it consumes.

Today’s business landscape is more complex than ever due to the increase in third-party apps leveraged for efficiency and productivity. Akamai reported in 2019 that 83% of internet traffic consisted of API driven app-to-app communication. Today, the majority of enterprises focus on securing the APIs they publish while overlooking the security of the far more numerous APIs they are consuming. According to 451 Research, large enterprises consume an average of 25,592 APIs. However, third-party vendors might publish anywhere from a handful of APIs focused on core functionalities, or even hundreds of APIs catering to a wide range of integrations and services. The APIs that are consumed often go unmonitored, creating a substantial gap in security measures.
The Risk
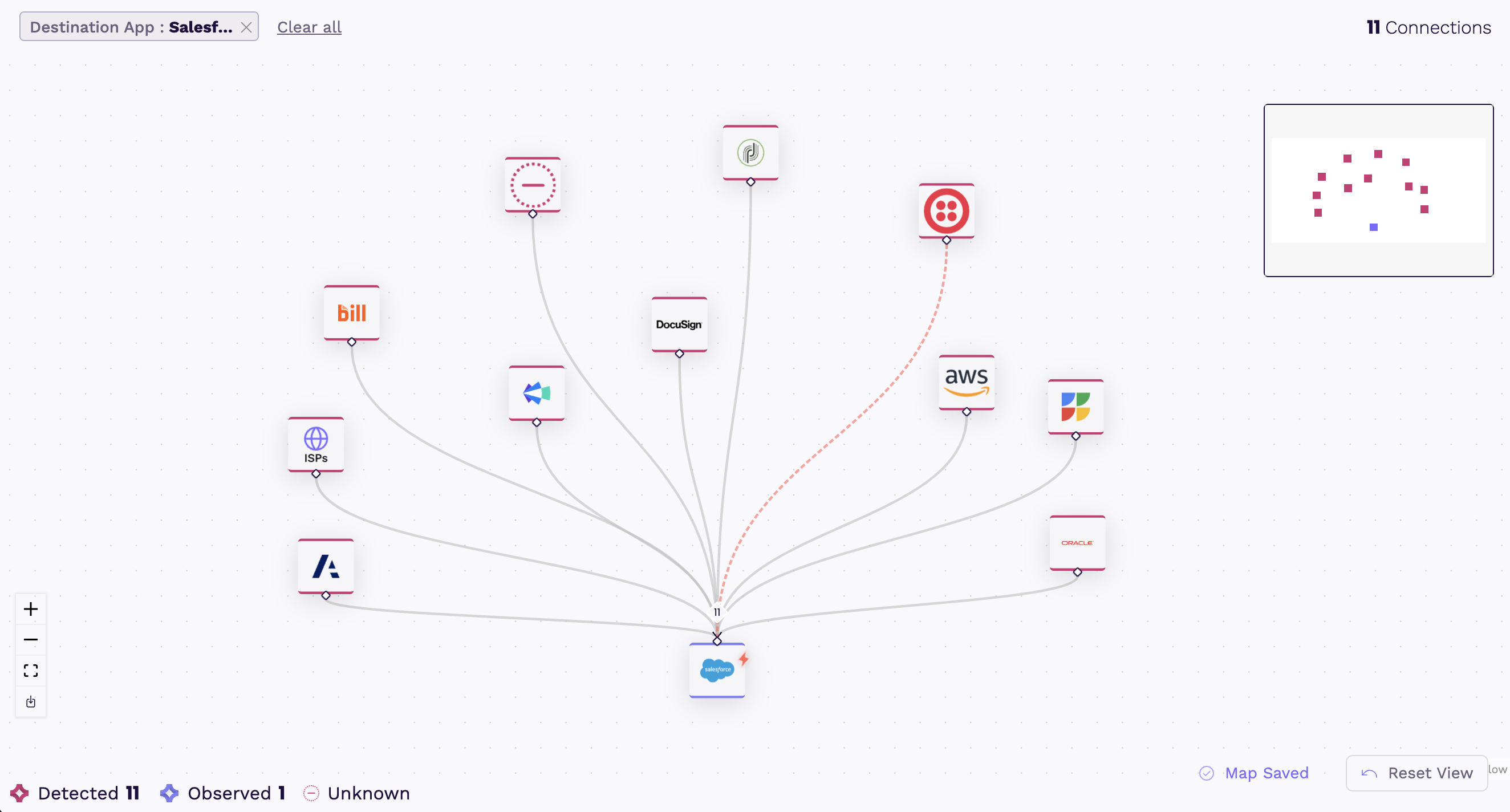
The risk lies within the way applications connect with each other. Above, Vorlon shows a mapping of a single app connected to eleven others.
Third-party apps, like their human counterparts, are granted access to other systems via API. In best practice, each connection has a unique access secret (also referred to as a key or token). In reality, these secrets are shared across multiple apps and users.
Vorlon also discovered an ITSM vendor using basic authentication in their APIs, allowing broad admin access without detailed controls. Conversely, our research team identified a leading CRM vendor with an exceptional approach to granular permissions, but their customers complained they lacked the ability to differentiate legitimate traffic and traffic from a stolen API secret before Vorlon.
Vorlon’s extensive analysis of over fifty of the most common business critical applications found the majority of APIs are built without granular controls. A common response is to encrypt the data, but encryption only protects against eavesdropping—Man-in-the-Middle attacks—not attackers with legitimate credentials.
Customers consuming third-party APIs face challenges with control and visibility, including:
- Understanding the extent of app access,
- Tracking the destination of their data,
- Differentiating between legitimate traffic and potential attackers who may have compromised an API secret.
For years, the answer was to run a vendor risk assessment at the time of purchase, and rely solely on the legal agreement for protection. This reactive approach is proving to be costly with fines in the six-digits for failing to protect customer data from leaks in third-party applications.
The Clock’s Ticking
Typically, it takes an average of 90 days to detect a breach and another 120 days to remediate. This gives attackers roughly seven months to run simple scripts to find API secrets or even procure this information on the dark web. In the meantime, the CIO and their teams—IT, security, GRC (governance, risk, and compliance), and data privacy—are burdened with protecting the organization without a tool to help.
So we asked ourselves–what if we could close that window?
“Being proactive and tackling risks posed by your vendors is not a simple problem to solve. Expecting an enterprise’s security team to do this work on their own is unrealistic,” says Vorlon CEO and Co-founder Amir Khayat.
The Solution
Our vision for the future of API Security expands the scope of what analysts and enterprises think the term covers. Today, API Security addresses just the tip of the iceberg. Enterprises spend millions of dollars to “shift left,” building security into the APIs they publish, but invest nothing into enabling the organization to monitor, detect, and remediate the APIs their organization consumes.
API Security must address both creator and consumer needs. For those consuming APIs, they need a way to:
- Detect all existing connections,
- Establish a baseline for what constitutes normal activity,
- Alert when abnormal behavior occurs in near real-time,
- Prevent data in motion from going where it doesn’t belong,
- Provide context and enhanced threat intelligence for faster investigations,
- Enable effective remediation strategies.
Vorlon’s Early Success
Vorlon has developed a way to quickly analyze third-party applications. Complete with detection, threat intelligence, and remediation capabilities, Vorlon enables security teams to significantly reduce the window of opportunity for attackers to exploit risks posed by third-party applications. “The patent-pending technology Vorlon has built is far superior to anything else we have seen in this space,” says Steve Loughlin, Partner at Accel.
What truly sets Vorlon apart is our patent-pending technology and our commitment to maintaining the largest catalog of monitored vendor apps. Currently, Vorlon is capable of identifying nearly one thousand third-party apps connecting to an enterprise.
Since November 2023, we have analyzed over 50 million API calls. Collaboration with early adopters has led to the discovery and remediation of critical issues including:
- Over permissive connections sharing unnecessary PII,
- Abuse of API secrets,
- Multi-use secrets connected to unknown applications,
- Access from malicious IP addresses,
- Abnormal activity from third-party applications.
“For an enterprise security team to replicate what Vorlon’s platform does on their own would require extensive dedicated resources and expertise in complex third-party apps and APIs,” says Vorlon CEO and Co-founder Amir Khayat. “This early success underscores the importance of investing in Vorlon, and our ability to transform enterprise data security,” he continues.
How It Started
Vorlon was started by cybersecurity experts Amir Khayat and Amichay Spivak. The two met as part of the founding team responsible for developing a Security Orchestration Automation and Response platform called Demisto which was acquired in 2019 by Palo Alto Networks—its third-largest acquisition to date.
A few years later, the former Palo Alto Networks co-workers both identified a critical gap in enterprise data security with no solutions on the market to solve it. They are joined by a hand-picked team of industry experts dedicated to developing the best solutions for modern security challenges.

Explore our website or request a demo to learn more.
For media inquiries, please contact:
Alex Yakubov
Vorlon, Head of Marketing
press@vorlonsecurity.com
+1 (415) 649-5462
https://vorlonsecurity.com